No industry or sector is immune to hacking. That reality was made painfully clear in mid-May, when a cyberattacker using WannaCry ransomware crippled health care institutions and many other kinds of organizations around the world. In 2015 over 113 million Americans health records were exposed, and in 2016 the number was over 16 million, according to reports submitted to the U.S. Department of Health and Human Service’s Office for Civil Rights. At the beginning of 2017 Experian predicted that the health care sector would be the most heavily targeted vertical industry. A March 2017 report from the Identity Theft Resource Center indicated that more than 25% of all data breaches were related to health care. The estimated loss to the industry is $5.6 billion per year. These stats should be a wake-up call for the entire industry.
There are three reasons health care is the source of so much stolen data right now. First, health care data can be monetized. For instance, cybercriminals can use medical data to sell fake identities, construct synthetic identities, and enable someone to conduct medical identity theft. If that doesn’t work, they can use the stolen information for traditional identity theft, since medical information tends to include enough information to allow a criminal to open a credit card, bank account, or loan in the victim’s name. If neither of those works, cybercriminals can use ransomware to extort health care organizations to pay them money to regain access to compromised systems and data.
Second, health care organizations have been slow to adopt practices that have worked for other industries. Most health care portals, for example, don’t have strong multifactor authentication. Many medical personnel are unaware of the risks to data security (which is ironic given the strong emphasis on patient privacy). And health care organizations tend to have smaller security budgets and teams than financial services organizations.
Finally, as other industries have become more sophisticated in detecting and blocking cyberattacks, criminals have had to find new sources of data. Aside from the fact that health care institutions collectively hold information on the vast majority of the population, their IT systems also have links to financial services (e.g., flexible spending accounts with their own debit cards or health savings accounts that can have five-figure balances after two to three years).
Here are some specific recommendations, which are based on our collective expertise in care delivery, health systems, financial regulation, and risk management.
Update HIPAA. Like the PCI DSS rules for debit and credit card security, the HIPAA Security Rule and the HIPAA Privacy Rule are already well-known frameworks for defining how a health care organization should secure its people, systems, data, and equipment. These established methods of approaching health care security would merely need to be updated to cover new forms of cyberattacks and new tactics employed by cybercriminals.
Take stock of basic housekeeping. Care providers should apply strong encryption to all patient data and limit who has permission to access medical charts. In addition, organizations should monitor searches and downloads from their IT systems by tracking exfiltrated data such as large batch files of patient, research, financial, or other sensitive data.
Purchase insurance. Many financial services organizations have cyber insurance, and health care systems should get it, too. Since this is a relatively nascent kind of insurance, most leaders of health care organizations and boards of directors may not be aware that it exists. Significant open questions about it remain, including who should pay for such policies and whether it should protect the institution, the patient, or both. At the moment, the institutions themselves are paying, and this likely will not change in the foreseeable future.
Require training for personnel. Human error, including falling for phishing attacks, is the leading cause of major security breaches today. Health care systems should regularly remind people of the importance of information security best practices through required training, strategic reminders, and other means.
Protect supply chains. Hospitals and health care systems have diversified supply chains and massive lists of vendors with whom they digitally interface. They are a tempting way for cybercriminals to gain access to health care organizations’ IT systems. Consequently, care providers must understand the many moving parts that are involved and protect their relationships and information exchanges with and among those groups. Third-party vendors can help assess such risks and recommend ways to minimize them.
Share industry best practices regarding cybersecurity. The FS-ISAC has made life easier and safer for the financial services sector by enabling peer financial institutions to share information rapidly and directly. Similar groups, such as the NH-ISAC, can serve as starting points for expanding similar types of discussions and planning.
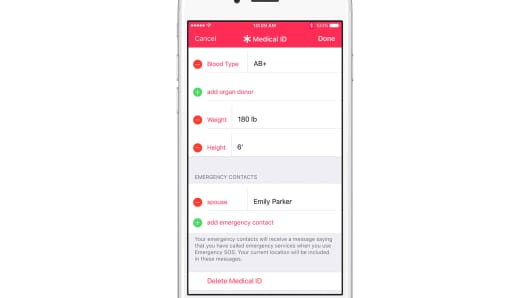
Deploy strong authentication. Health care systems should use multifactor authentication or other types of consumer security that are already ubiquitous in the U.S. financial services arena. Most U.S. consumers are already familiar with this type of technology and won’t need to be significantly reeducated (a challenge the financial services sector had to deal with a decade ago).
Adopt “tokenization.” This approach, which involves substituting sensitive data with other unique but nonsensitive data, has been in vogue in the credit card world for the past few years. It is a suitable way to protect data in situations in which a consumer (i.e., a patient) is involved in some type of card-based transaction. This might involve using a flexible spending reimbursement card or paying a health care–related bill online.
Copy the chip card approach. The U.S. consumer first encountered chip cards in a significant way in early 2015, when card issuers began to widely distribute them. Much of this was done in the run-up to a shift in who was liable for fraud. U.S. consumers are now intimately familiar with how to use such cards. (The cards have been in use for many years in France, the UK, Canada, Australia, and elsewhere.) Public and private payers are discussing the merits of issuing chip cards to beneficiaries to expedite patient identification and eligibility verification.
Experiment with blockchain. The technology can record transactions between two parties efficiently and in a verifiable and permanent way. It is being used in financial services as well as other areas. For instance, after Estonia suffered a significant cyberbreach in 2007, the country became more aggressive about protecting its society and is now using blockchain to protect its citizens’ medical data. A number of blockchain-based identity-credentialing systems exist, including Guardtime, TruCred, Civic, and OneName.
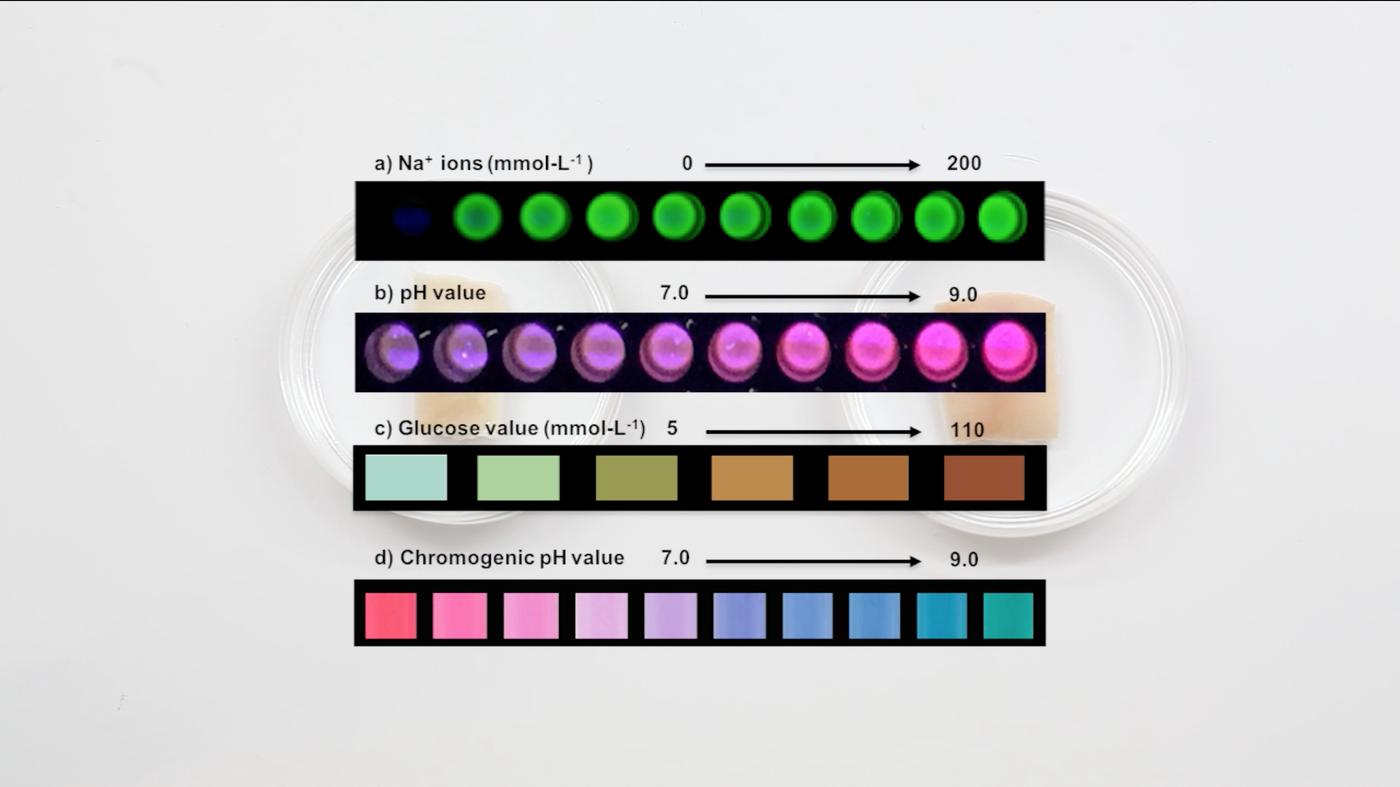
Consider biometric-based security. Biometrics are increasingly being embraced as the ultimate “bio-identifier.” Start-ups such as Simprints and RightPatient are testing its value as a verification feature for electronic medical records. Perhaps the most ambitious application of biometrics is the Indian government’s Aadhaar project, which has created 12-digit unique identity numbers based on biometric and demographic information (e.g., iris scans, digital fingerprints, and a digital photo) for nearly all of the country’s 1.2 billion citizens. But underlining the sad reality that no system is totally safe, this new system has already faced difficulties: Last month, the Centre for Internet and Society reported that 130 million Aadhaar numbers and around 100 million bank numbers of beneficiaries have been leaked online.
The great boon of the digital era has been that patients’ medical data is becoming increasingly portable. This promises to make it vastly easier to collect and share data from all the players in health care in the years ahead. But, unfortunately, it also poses major cybersecurity risks.
In this new world, protecting patients’ health information in accordance with HIPAA will take a highly coordinated effort among care providers, insurers, and institutions, as well as significant investments in new tools and practices. It also will require health care institutions to look at the cyber risks across their business, not simply in one niche area (e.g., access to patient records). In the risk management world, that is known as taking a holistic approach.
The health care sector needs to adopt lessons from industries, such as financial services, that are much more advanced in their ability to thwart cyberattacks. Given how badly health care organizations are lagging others, they must make boosting cybersecurity a priority.











 Xin LIU, Katia Vega
Xin LIU, Katia Vega



Recent Comments